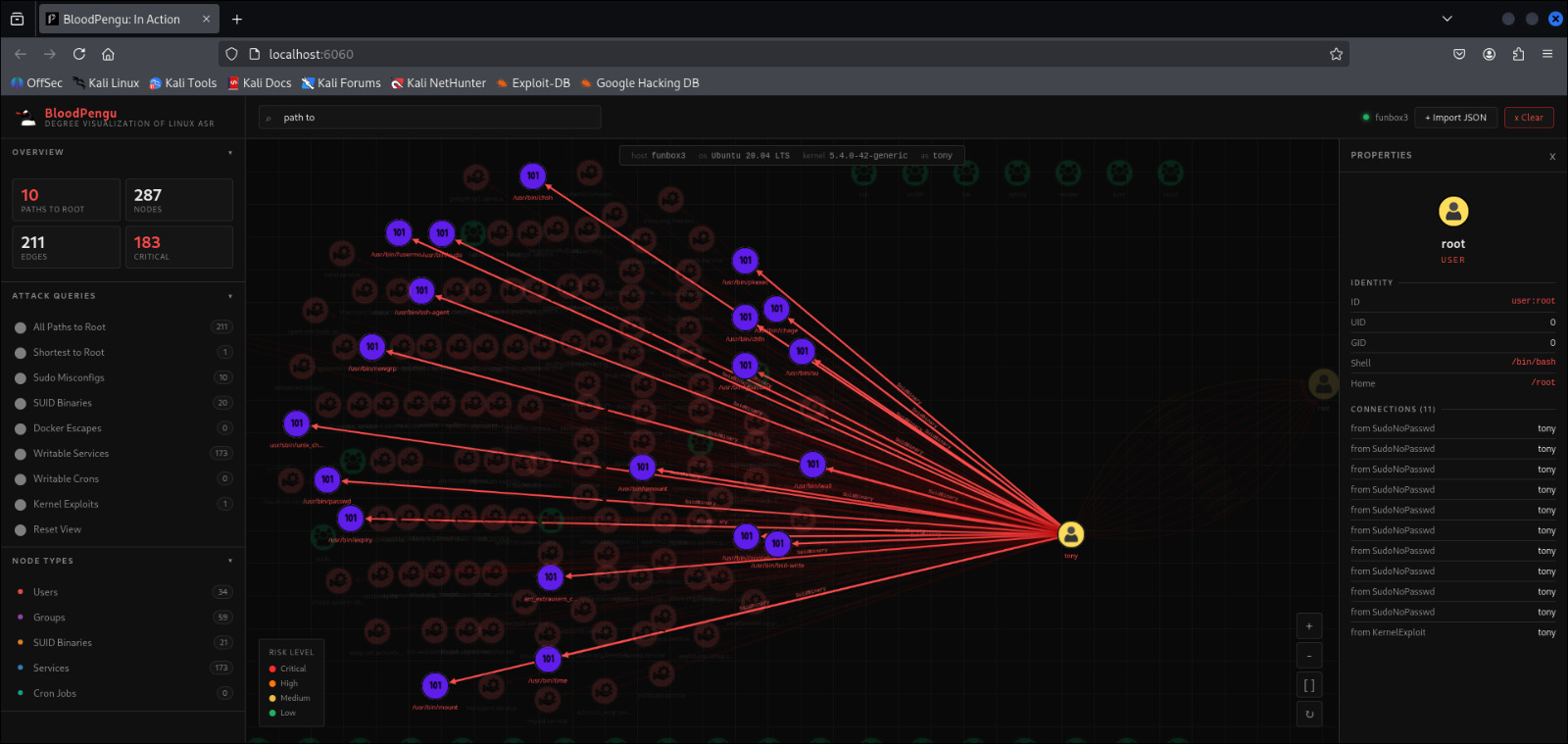
BloodPengu in action.
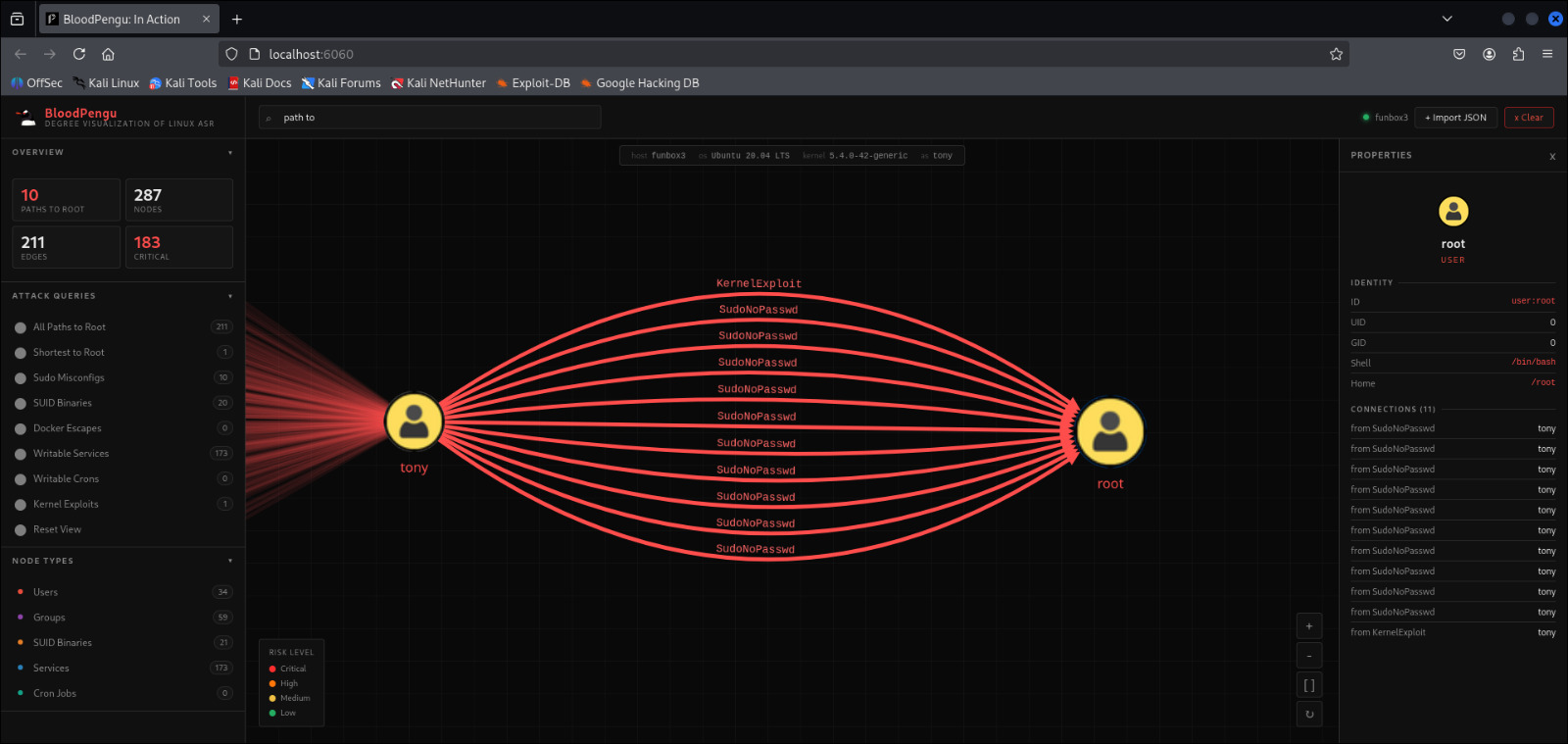
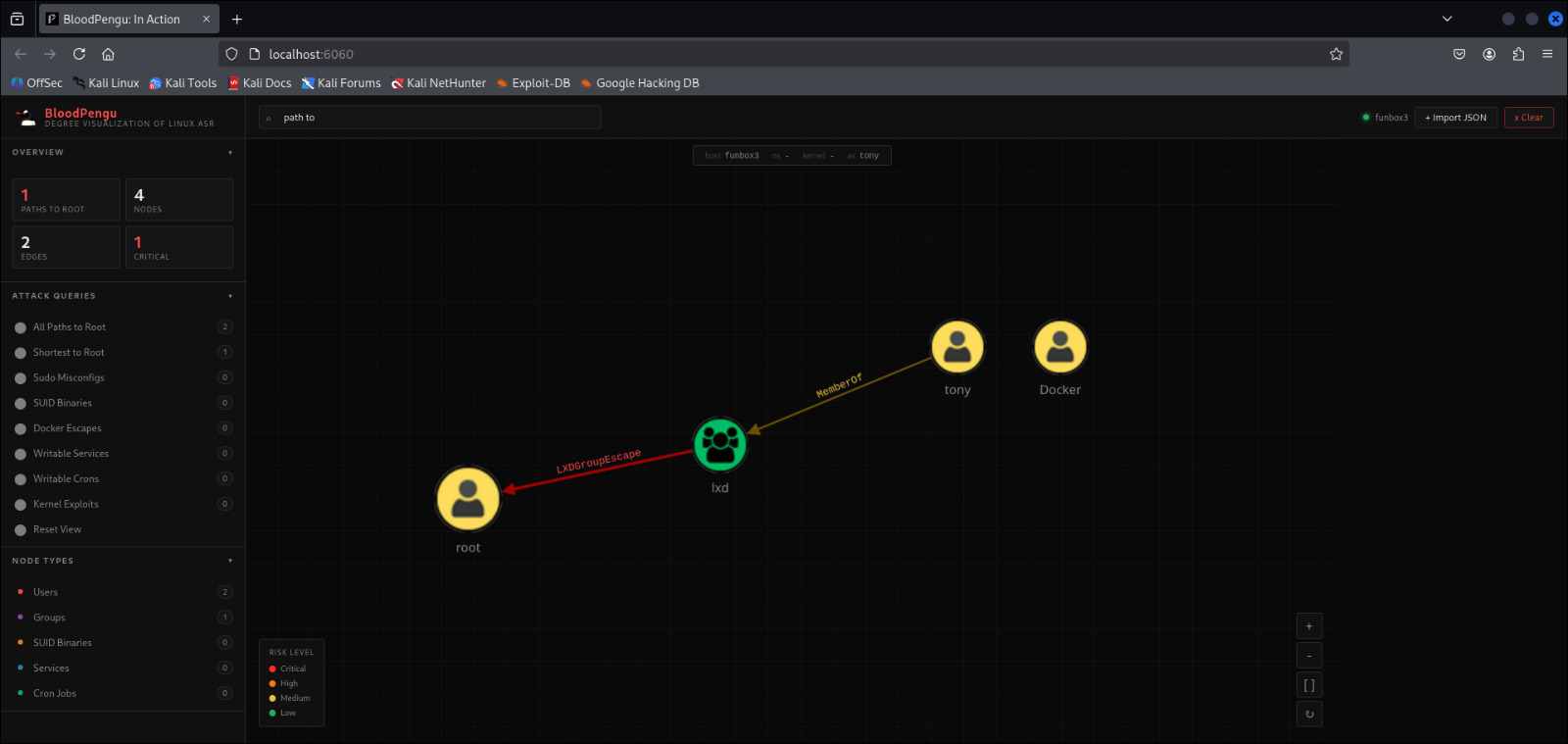
Real attack paths. Real Linux environments. Every node clickable. Every edge labeled.
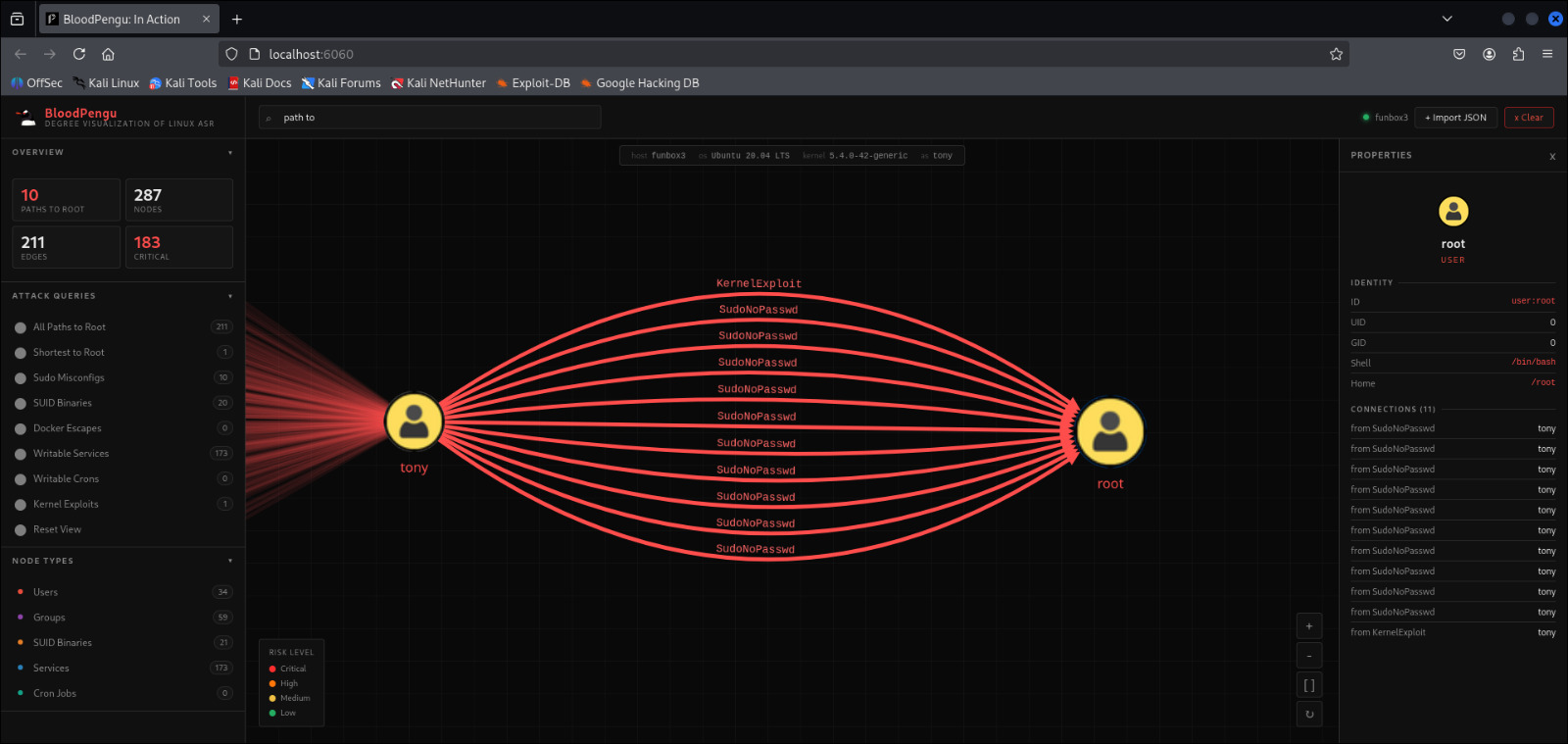
Graph based privilege escalation modeling for modern Linux environments. Visualize attack-paths to root before your adversary.
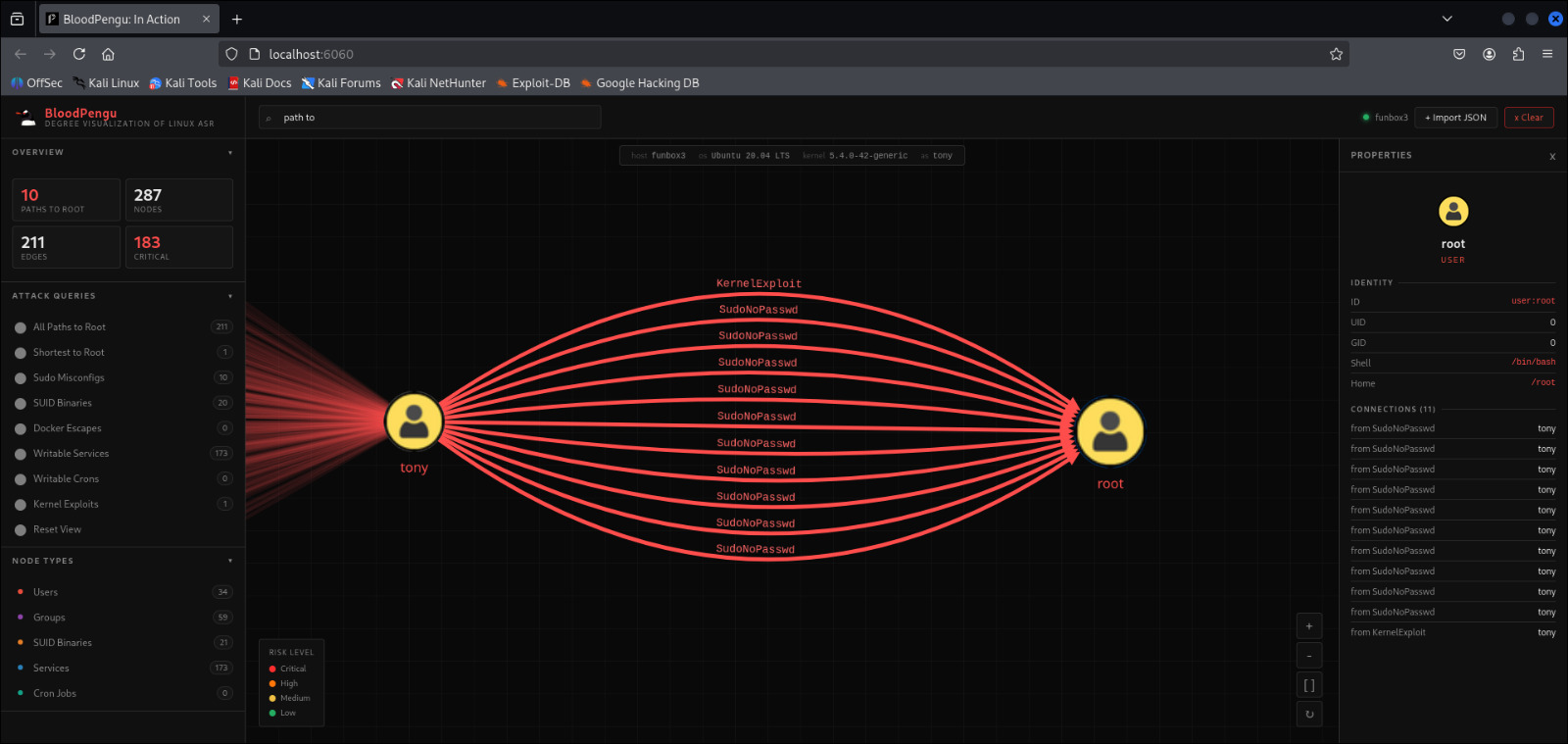
Identify Hundreds, even Thousands of Attack-paths. BloodPengu brings graph-based ASR to Linux/Unix environments.
Collects Data with PyPengu on target, enumerating privilege vectors, mapping group relationships, and surfacing escalation paths. BloodPengu ingests JSON's data and renders it as an interactive attack graph.
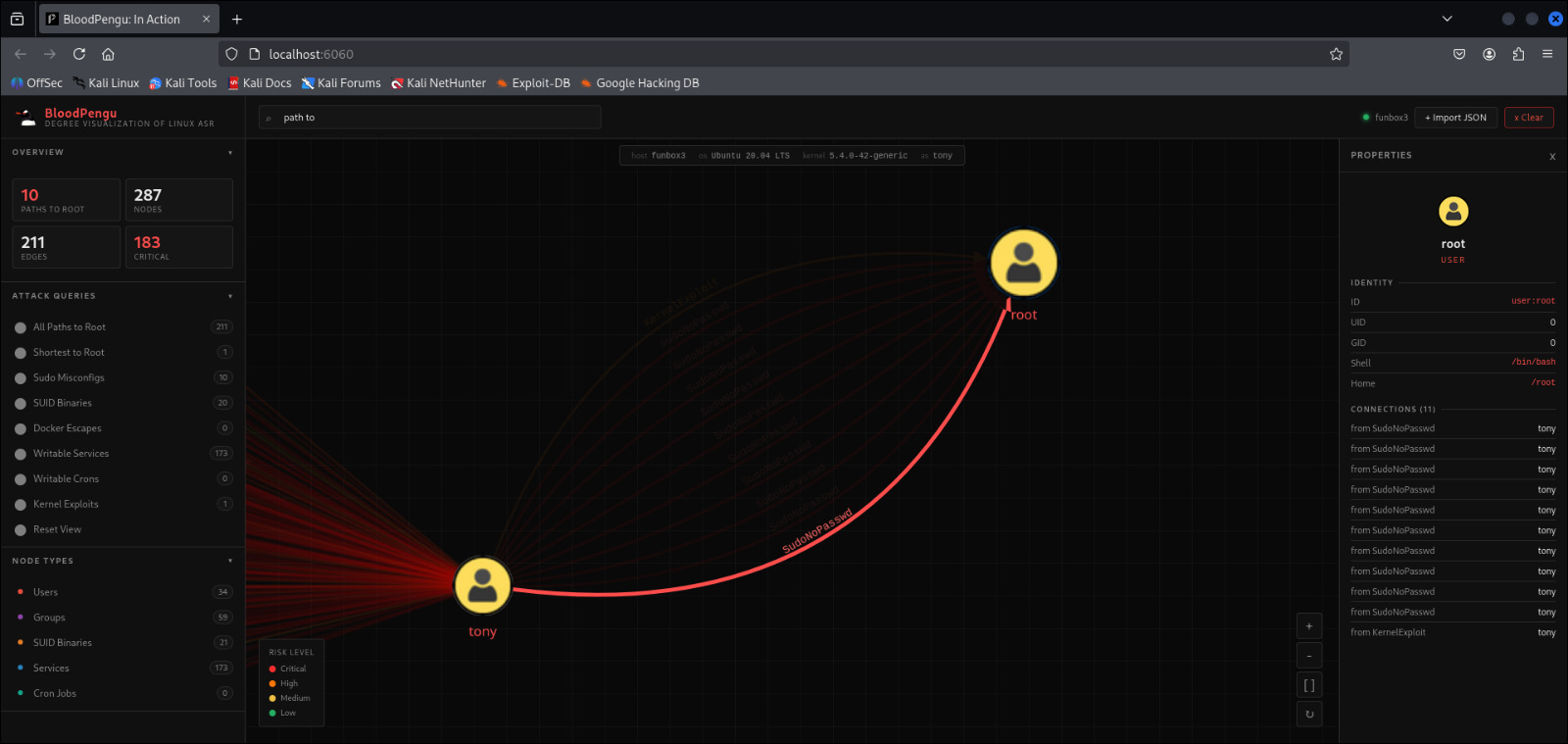
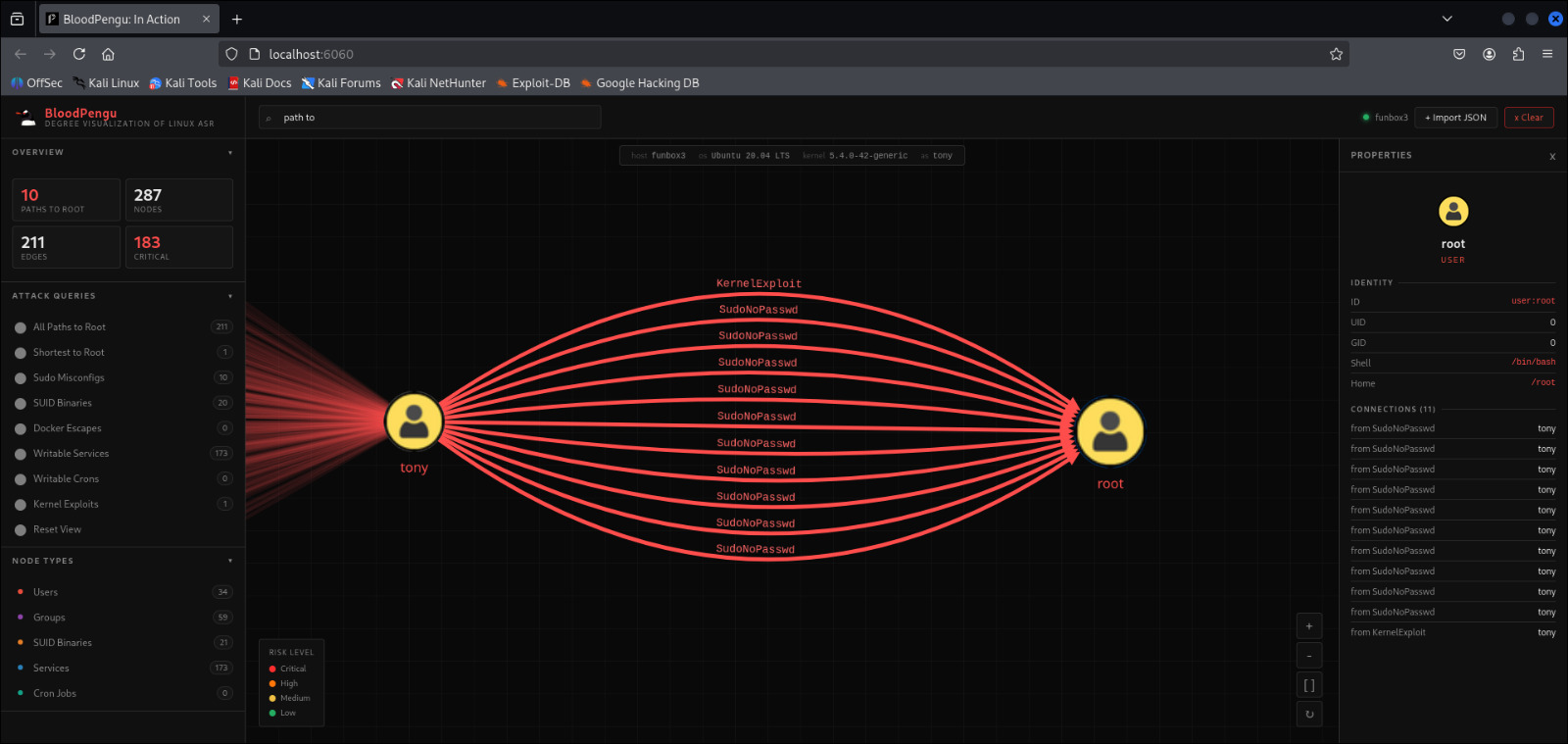
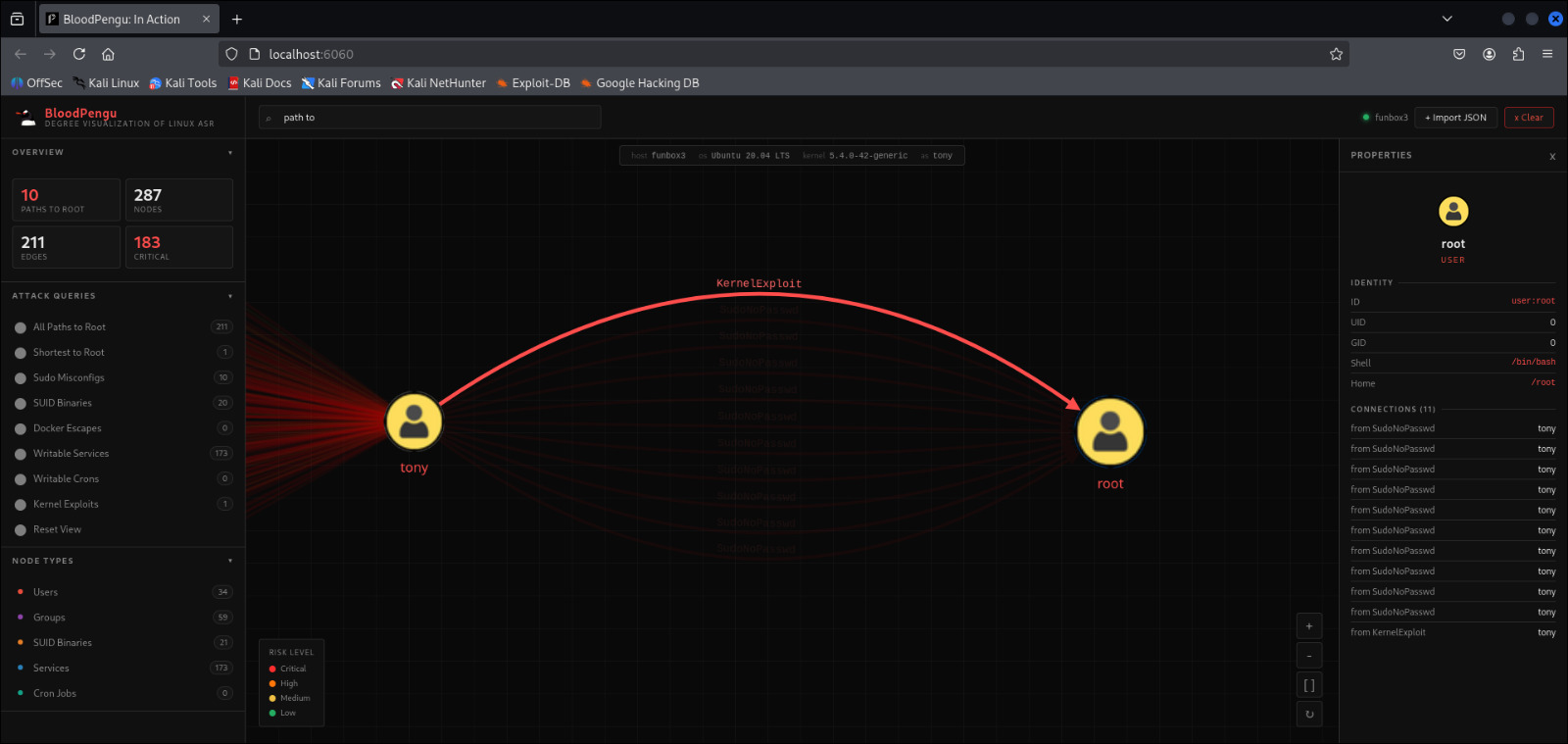
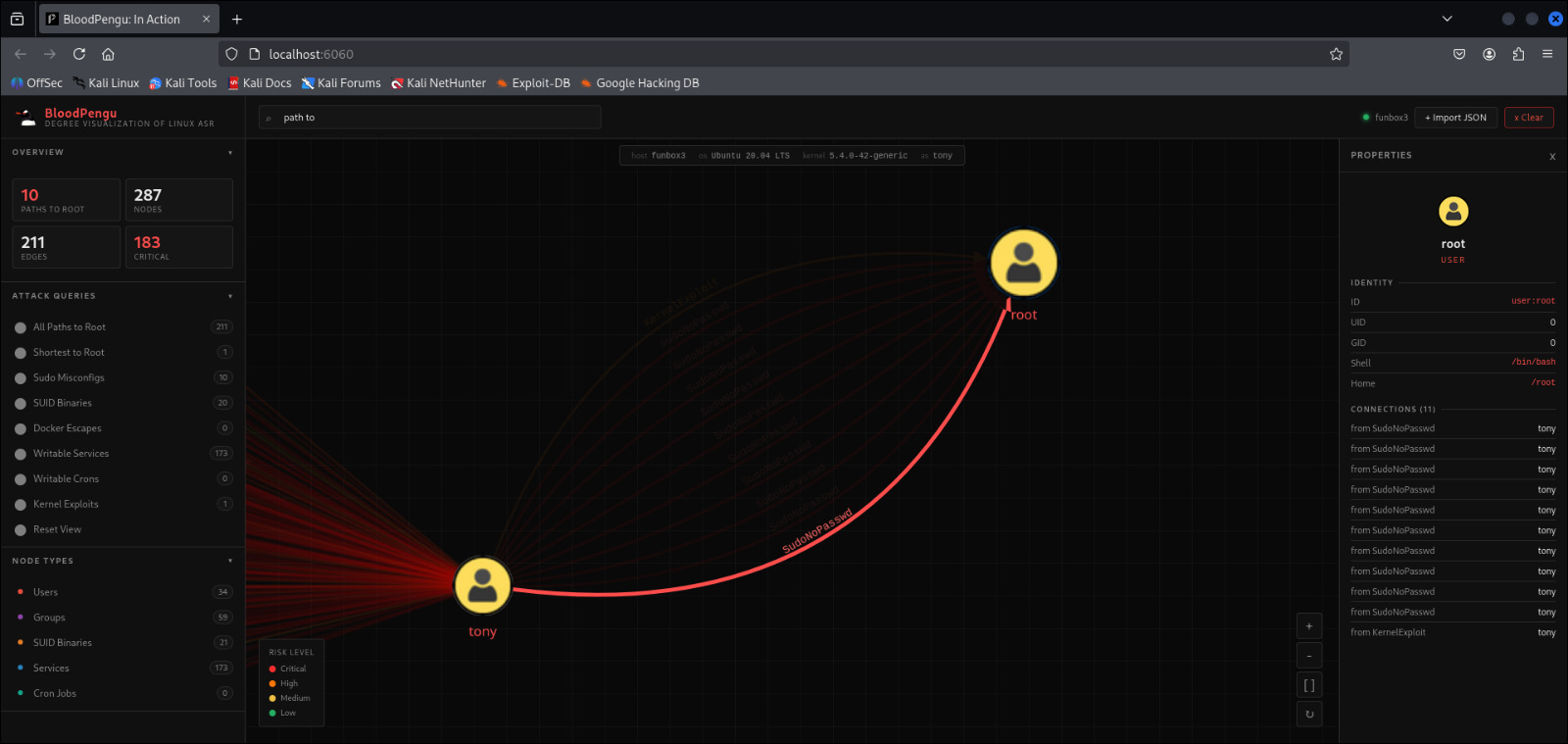
Security can identify the shortest path to root in seconds. Defenders can map and close attack paths before they are exploited.
BloodPengu maps every privilege escalation path across your Linux attack surface into a unified, queryable graph.
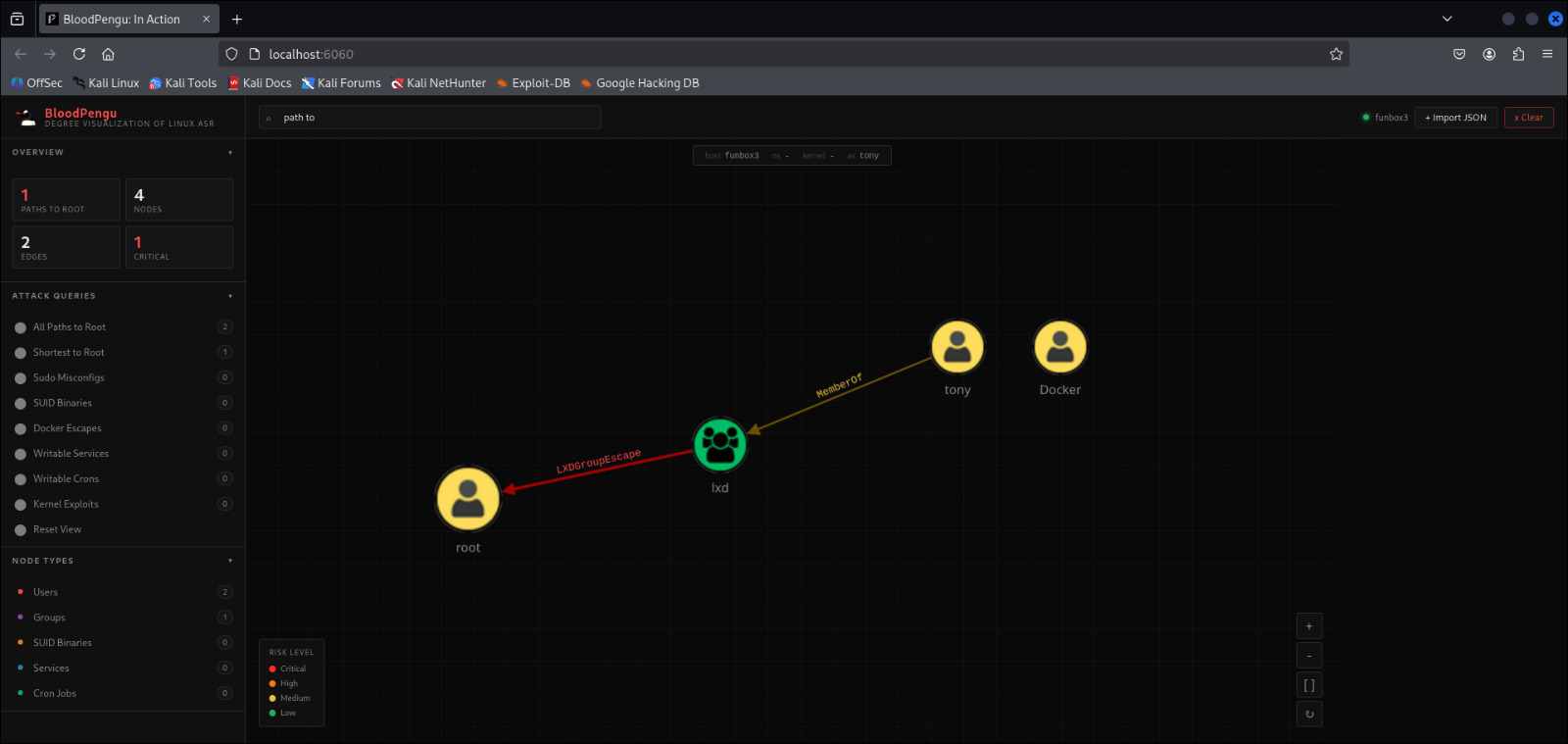
Visualizes group membership depth and privileged inheritance. Surfaces dangerous groups like docker, lxd, disk, and sudo with full escalation impact.
Parses sudo/root access output and NOPASSWD rules. Maps direct and indirect escalation paths through sudoers misconfigurations and dangerous binary configurations.
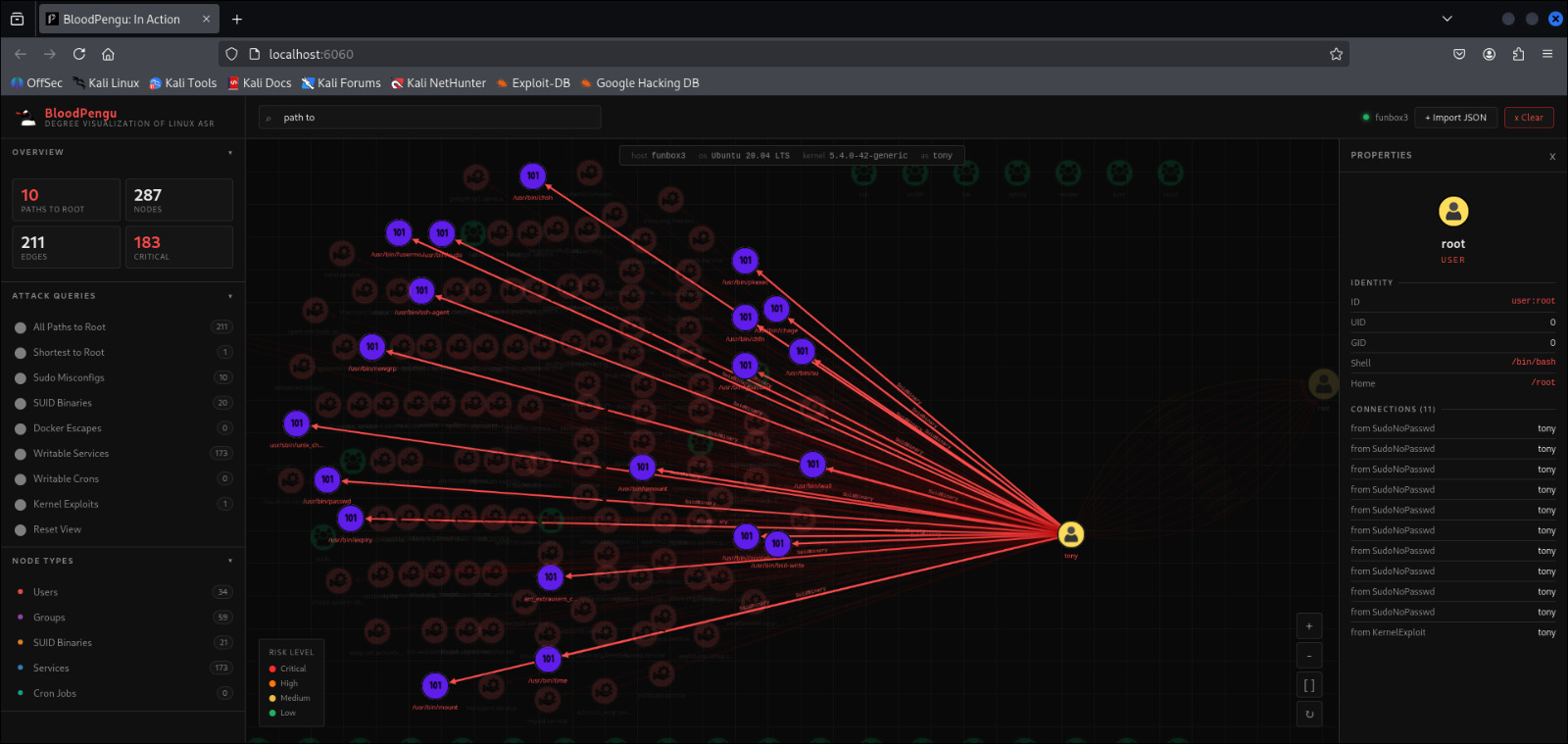
Identifies writable systemd service unit files and scripts executed with elevated privileges that can be hijacked across user boundaries.
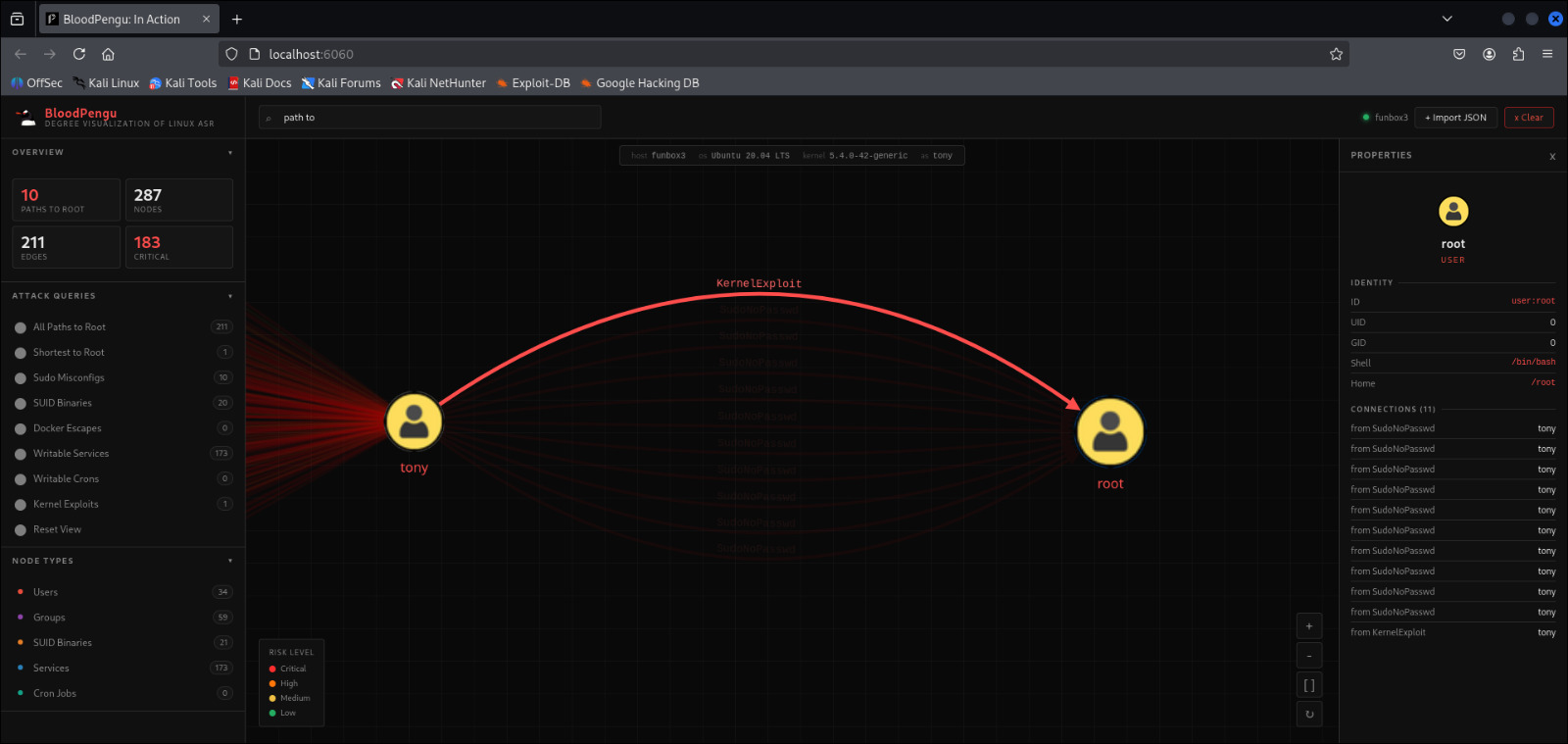
Captures kernel version and cross-references known CVEs. Maps KernelExploit edges including DirtyPipe, DirtyCow, and overlayfs privilege chains.
Enumerates all SUID and SGID binaries across the filesystem. Cross-references against GTFOBins-style exploitable binaries to surface immediate escalation vectors.
Detects container group membership and maps container escape paths. Identifies LXDGroupEscape and DockerEscape vectors with full graph visualization.
Real attack paths. Real Linux environments. Every node clickable. Every edge labeled.
A two-component pipeline. PyPengu runs locally on the target and enumerates the attack surface. BloodPengu ingests that JSON and renders an interactive attack graph.
Run the static Go binary on target. No dependencies. Supports x86_64, ARM64, x86. Outputs pypengu-output.json.
8 core collectors run in parallel across sudo, SUID, docker, services, cron, kernel, groups, and users. All findings serialized to JSON.
Drop the JSON into BloodPengu via the Import JSON interface. The graph auto-populates with nodes, edges, and risk levels.
Run pre-built queries: Shortest to Root, All Paths to Root, Sudo Misconfigs, SUID Binaries, Kernel Exploits, and more.
Run PyPengu. Import the Digested Data. See every path to root before your adversary does.